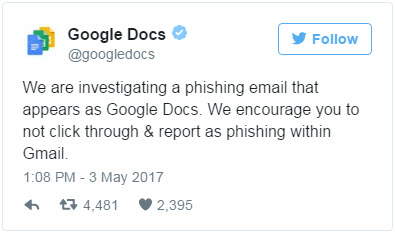
Google confirmed the validity of the latest phishing attack which targets Gmail users. This attack seeks to gain control of users' email histories and then spread itself to all of their contacts. The worm arrives in users' inboxes posing as an email from a trusted contact and then asks users to check out an attached "Google Docs," or GDocs, file. Clicking on the link takes you to a real Google security page, where you are asked to give permission for the fake app, posing as GDocs, to manage users' email account.
To make things worse, it also sent itself out to all of the affected users' contacts (Gmail or otherwise) reproducing itself hundreds of times whenver someone fell for it.
The strategy is a common one, but this particular worm caused havoc for millions of users because of its unusually sophisticated construction. Not only did the malicious link look real, but the email that delivered it also appeared to come from someone users already knew. On top of this, the payload manipulated Google's real login system!
It could have been a potential calamity for unsuspecting victims. With control of your Gmail account, scammers could harvest any personal data you've ever sent or received in an email. This can allow them to generate password-reset requests on scores of other services, potentially letting the hackers take over any of your other accounts (like Amazon, Facebook, Instagram, Netflix, or online bank accounts).
What you can do
While the malicious email was a dead ringer for a real message from a trusted friend, there was one key giveaway: the email was sent to a fake email address in the main recipient field — hhhhhhhhhhhhhhhh@mailinator.com. Users' addresses were included in the BCC field.
If you received this email, simply delete it. As always, do NOT click on a link that you're not 100% confident in where it came from and where it will take you.
If you unfortunately fell for the scam and granted permission to the hackers, go to your Google connected sites console and immediately revoke access to "Google Docs." If you don't trust the embedded link here (which is generally a good practice), you can manually type the address into your browser: https://myaccount.google.com/security?pli=1#connectedapps.
Lastly, go change your Google password.
This is another example of the new technology paradigm we're living in. Security vigilance is needed everywhere. Yet another reason to implement security training for your staff.
What do you think? Has this info been helpful? Let us know in the Comment box below or shoot me an email if you’d like to chat about this in more detail.
/fpa-logo-tagline.gif)







